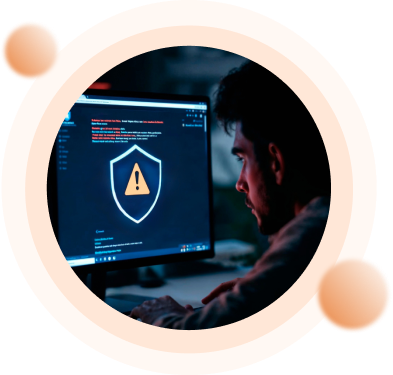
Threat modelling is a structured process to identify the security requirement and pinpoint security Threats are potential vulnerabilities that may occur with various methods. Threat modeling works by identifying the types of threats that may cause an application or computer system. It adopts the perspective of malicious hackers to see how much damage they could do. When conducting threat modeling, organizations analyze software architecture, business contacts, and other artifacts. This process enables a deep understanding and discovery of important aspects of the system. It typically conducts threat modeling during the design stage of a new application to help the developers easily find the vulnerability and become aware of the security implications of their design code and configuration diseases.
The first step is to identify the organization's assets, both physical and digital.
The next step is to identify the threats to those assets. This includes both internal and external threats.
The third step is to assess the likelihood and impact of each threat. This helps to prioritize the threats that need to be addressed first.
The fourth step is to develop mitigation strategies for the threats. This could involve implementing security controls, changing processes, or training employees.

As a threat modelling service provider, we offer a variety of services to help organizations identify and mitigate security risks. These services include the following:
These workshops help organizations understand the threats to their systems and assets.
These assessments help organizations identify and assess the likelihood and impact of threats.
These tools help organizations automate the threat modeling process.
This training helps organizations learn how to conduct threat modeling.
This is a threat modeling methodology that focuses on the assets, threats, and likelihood of attacks.
This is a threat modeling methodology that focuses on the six types of threats: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege.
This is a threat modelling methodology that focuses on the OWASP Top 10 vulnerabilities.
For all your threat modeling needs, Nishaj is right here to help.
A proactive security design approach to identify and mitigate risks early in development.

Nishaj Infosolutions Pvt. Ltd. is a cyber security and compliance consulting company based in India that helps businesses assess, improve, and secure their IT infrastructure, manage risks, and achieve compliance with global standards.
We offer a wide range of services, including:
Vulnerability Assessment and Penetration Testing (VAPT) involves identifying security weaknesses and simulating cyber-attacks on systems to find vulnerabilities before hackers do. It helps organizations strengthen security posture and protect sensitive data.
ISO 27001 is an international standard for information security management systems (ISMS). Nishaj offers advisory, assessment, gap analysis, implementation, and support to help organizations achieve and maintain ISO 27001 certification.
SOC 1 and SOC 2 reports ensure that your organization meets strict standards for controls related to financial reporting (SOC 1) and trust service criteria like security, confidentiality, and privacy (SOC 2). Nishaj provides assessment, implementation support, and reporting services for SOC compliance.
Yes. We provide cyber security consulting, VAPT awareness training, and compliance readiness training to help your team understand threats and strengthen defenses effectively.
Our services are valuable for organizations of various sizes and industries that need to secure their digital assets, comply with regulations, and manage risks — including IT, finance, healthcare, legal, and more.
Simply contact us through our website’s contact form or call us to schedule an initial consultation. A Nishaj expert will connect with you to understand your requirements and propose the best solution.
We offer tailored, cost-effective solutions backed by a strong team of specialists, comprehensive service offerings, and real-world experience in helping businesses improve security posture and compliance.
Yes. We provide flexible engagement models that include remote assessments, on-site services, and hybrid support depending on your needs, ensuring minimal disruption to your operations.
We help global leaders with their organization’s most critical issues and opportunities. Together, we create enduring change and results.
Privacy Policy | © NISHAJ INFOSOLUTIONS PVT. LTD. 2021 All Right Reserved.